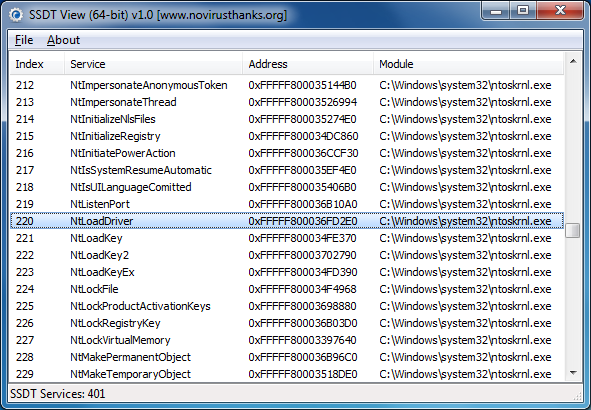
SSDT View is free software that designed to list the most significant aspects of the System Service Descriptor Table (SSDT) including service indexes, service addresses, service names and the module name which corresponds to the service address.
Whenever a program carries out some core function in Windows – checks the Registry, reads a file, launches or closes a process and more – Windows will usually pass the command to the relevant function in the SSDT: NtReadFile, say, or NtWriteFile. And so if malware can tweak the table, change one of these memory addresses to point to its own module instead, then it’ll be able to take very low-level control of your system, perhaps hiding itself from antivirus software or protecting its processes from termination.
[advt]If you suspect your system is infected by malware, then, checking the SSDT for hooks can be a useful step. Anti-rootkit tools can do this for you, but they can be complex and intimidating: SSDT View is much safer and more straightforward, particularly if you’re a novice in this field. This utility can be useful for listing table hooks despite the fact that x64 OS ships with KPP/PG-ready kernels, which translates to the kernel bug checking if the SSDT is modified.

Be the first to comment