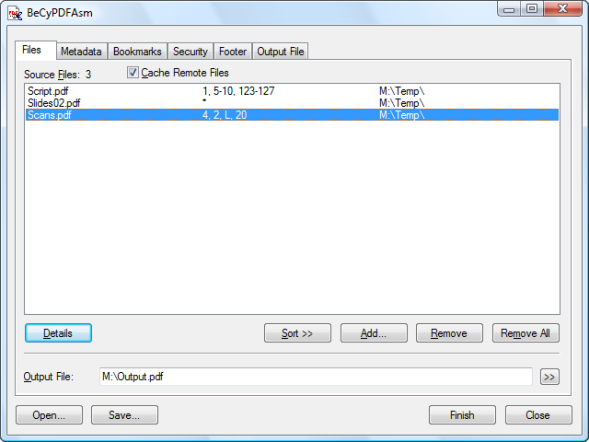
BeCyPDFAsm utility is a graphical add-on for the command-line tool mbtPdfAsm. mbtPdfAsm allows extracting individual or several pages from one or more input documents to assemble a new PDF document from those pages. BeCyPDFAsm assists in configuring such a job by means of an intuitive dialog-based user interface and calls mbtPdfAsm behind the scences. This way, the end user is saved from learning the proper command-line usage. If mbtPdfAsm.exe is not stored in the same directory as BeCyPDFAsm, a configuration file may be used to tell BeCyPDFAsm the installation path to mbtPdfAsm.
Features
[advt]Multi Document Processing
BeCyPDFAsm uses the script option of mbtPdfAsm to extract arbitrary pages from an arbitrary list of input PDF documents. The order of the input documents can easily be changed via drag&drop or simply be selecting ascending/descending order by file name.
Duplex Reconstruction
Using an assistant, one can re-assemble the odd and even pages of a document that has been scanned single-sided in a two pass process.
Metadata
When assembling new PDF documents, the info fields author, title, subject and keywords can be customized by the user.
Those inputs can either be typed in manually in the dialog or they can be captured from an existing PDF document prior to customization.
Bookmarks / Outlines
The new PDF document can optionally be supplemented with bookmarks. These bookmarks can be used to build a hypertext-like hierarchical index of the document’s content that allows readers to quickly access specific text locations.
Security
The produced document can be encrypted using a password to protect it from unauthorized access. Furthermore, an encrypted document can specify permissions that control what operations an authorized reader may perform.
Footer
A user-defined footer can be added to simple PDF documents. This can either be an arbitray text string or an automatically generated page index.
Split Mode
One can limit the maximum number of pages per output document to generate multiple smaller files instead of one big file.
Saving/Loading of Compositions
All dialog settings can be saved into compositions and later reloaded to quickly perform recurring jobs.
Passwords are saved in these files, too. Although the passwords are not directly readable, there is no serious cryptographic protection.

Be the first to comment